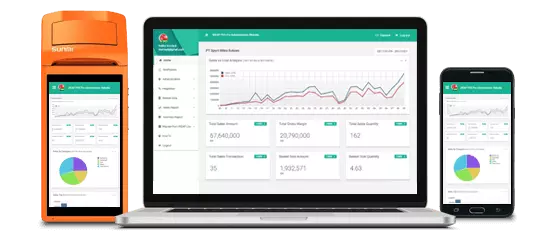
Kenali aktivitas toko dalam genggaman jari anda.
Laporan & Analitik, Realtime, Kapan Saja, Darimana Saja

Akses ke laporan konsolidasi untuk seluruh toko di Web Dashboard kapanpun dan dimanapun.
Dapat berjalan secara OFFLINE pada saat koneksi internet tidak tersedia
Semua Transaksi, Penerimaan Barang, Penjualan eceran, Pengeluaran barang terkonsolidasi dengan cloud ketika koneksi internet tersedia. Jika Koneksi internet tidak tersedia, transaksi akan tersimpan sementara dan otomatis disinkronisasi ketika Internet terkoneksi sehingga tidak ada kendala bisnis/ : Forensic researchers use these timestamped, numbered files

Data Toko, User, Produk, Pelanggan, Pemasok, Harga akan secara otomatis tersinkronisasi dari dashboard Web dan Aplikasi Mobile

QRIS untuk transaksi E-Money & otomatis rekonsiliasi : Analysis of the DownloadService or History databases

Mengatur toko anda dimanapun dan kapanpun!
Daftar Perusahaan /Badan usaha anda, Toko dan Administrator dalam 5 Langkah Mudah
Mengatur Kategori Barang, Pemasok, Pelanggan, Master data Barang, dan Harga jual kapanpun dan dmanapun anda baik di Web ataupun Aplikasi Mobile. Mengatur dan Sinkronisasi otomatis ke seluruh perangkat Mobile POS
Penetapan user ke toko tertentu dengan hak akses yang sesuai
Admin, Manager, Supervisor, Cashier: Forensic researchers use these timestamped, numbered files in the Downloads folder to reconstruct a timeline of user activity [2, 3].
While there is no single "famous" academic paper with this exact title, this specific file naming convention is frequently discussed in and cybersecurity research regarding:
If you are looking for a specific study, it may be a or a CTF (Capture The Flag) write-up where "Download Express(3).txt" was a key piece of evidence used to prove a user's intent or a system compromise.
: Security papers often reference these filenames when analyzing "drive-by downloads," where a user might unintentionally download a malicious script multiple times while trying to get a site to work [4, 5].
: Analysis of the DownloadService or History databases in Chromium-based browsers explains how these strings are generated and stored as persistent metadata [1, 6].
Apa yang Pengguna Kami Katakan Mengenai Aplikasi Kasir Android iREAP PRO
: Forensic researchers use these timestamped, numbered files in the Downloads folder to reconstruct a timeline of user activity [2, 3].
While there is no single "famous" academic paper with this exact title, this specific file naming convention is frequently discussed in and cybersecurity research regarding:
If you are looking for a specific study, it may be a or a CTF (Capture The Flag) write-up where "Download Express(3).txt" was a key piece of evidence used to prove a user's intent or a system compromise.
: Security papers often reference these filenames when analyzing "drive-by downloads," where a user might unintentionally download a malicious script multiple times while trying to get a site to work [4, 5].
: Analysis of the DownloadService or History databases in Chromium-based browsers explains how these strings are generated and stored as persistent metadata [1, 6].
Tim kami dapat dihubungi dari Senin sd Jumat , dari pukul 8:30am sampai 5:30pm, GMT+7 time