
Download oLQEAbe Ojb Khpul1Lba2g9Rxor1Mcd zip
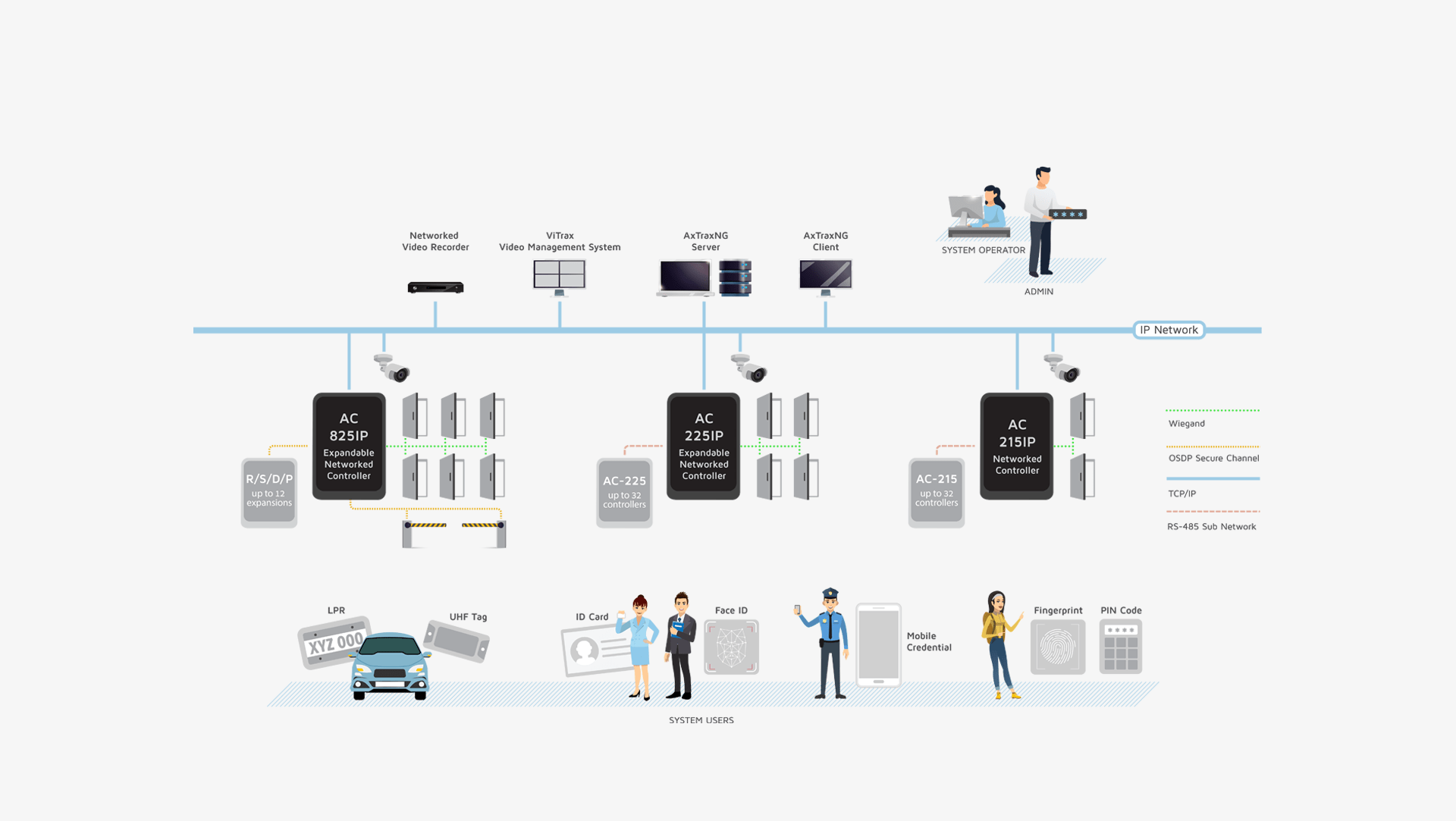
AxTraxNG is a complete server-client software management that enables setting physical access control policy across organizations that is available in multiple languages and date formats. The server manages thousands of networked access control panels and system users. The user-friendly interface is intuitive, reliable and rich in
functionality. With Rosslare’s SDK tool AxTraxNG also leverages easy integration and deployment of various
applications in security, safety, time and attendance and more. AxTraxNG allows the control and monitoring of
every aspect of site access.
Product Datasheets Development Tool
ZIP files are dangerous because they are "containers". While the archive itself might not be malicious, it can hide executable scripts ( .exe , .js , .vbs ) or that only activate once the file is extracted and opened. Some advanced malware, like the "ZIP bomb," uses extreme compression to pack gigabytes of data into a tiny file, which can crash your system when you try to open it. 2. Evasion Tactics Scammers use randomized names for several reasons:
In the modern digital landscape, files with gibberish or heavily randomized names—like "oLQEAbe Ojb Khpul1Lba2g9Rxor1Mcd.zip"—are often a major red flag for . These files are frequently used in phishing emails, sketchy forum posts, or via "drive-by downloads" where a site automatically attempts to save a file to your computer. 1. The Hidden Contents of ZIP Archives
While "oLQEAbe Ojb Khpul1Lba2g9Rxor1Mcd.zip" appears to be a specific file name, it is highly likely or a malicious file due to its randomized, nonsensical name . Cybercriminals frequently use randomly generated strings to bypass security filters or create unique links for phishing campaigns. Download oLQEAbe Ojb Khpul1Lba2g9Rxor1Mcd zip
Below is an essay discussing the dangers of downloading such files and how to handle them.
Some attacks involve fake websites that look like legitimate tools, such as the 7-Zip archiver, but serve trojanized installers instead. 3. Best Practices for Protection ZIP files are dangerous because they are "containers"
Unique names make it harder for email security filters to recognize the file as a known threat.
A user may mistake the complex name for a "system update" or an "encrypted document" they were meant to receive. such as the 7-Zip archiver
If you have already downloaded a file with a suspicious name, follow these steps to stay safe: Fake 7-Zip downloads are turning home PCs into proxy nodes